PEAP-MSCHAPv2 is hopefully on the way out since it's slow, broken and cumbersome. Still, it's widely used and I do not see that changing in the near future. Organizations will need to have some form of PKI and other will need to begin retiring aging devices that do not support EAP-TLS (WPA2 or 3).
Since its so common and the fact I deal with a lot of troubleshooting issues related to this authentication method, I decided to make a post about it. This is going to focus primarily on the wireless side, between the supplicant and authenticator. If you’d like to learn about the wired side of things I found this blog post during my research.
First we’ll introduce the message exchange ladder to understand the shear amount of messages needed to completely authenticate the client. This hints at why this method is slow compared to other methods.
http://revolutionwifi.blogspot.com/2010/09/peapv0-packet-flow-reference.html
We’ll skip over the initial connection and start with the method selection. If you would like a refresher I wrote about it here. EAP Type Selection
Depending on the client this does not have to contain identifiable data.
The next 3 frames show the radius server presenting the authentication method and client
Frame 10 is the most interesting of the bunch. We see the RADIUS server requesting the desired authentication method and providing the Challenge.
Frame 11 has the client responding with its desired authentication type.
Frame 12 is just a final acknowledgement from the Authentication Server Setting up the Tunnel
Referring back to our diagram we are now going to setting up our outer tunnel for the inner method. There's a few interesting frames here that I will mention and expand on.
Frame 13 contains lots of good information about the client capabilities and used for troubleshooting connectivity problems, similar to an Association Request. Something else to note is this particular Intel AX201 NIC apparently is still using a deprecated field.
The two areas I would like focus on are the Cipher Suites and Signature Algorithms (Hashing)
Knowing the above we can quickly validate if a client is capable of connecting to various networks.
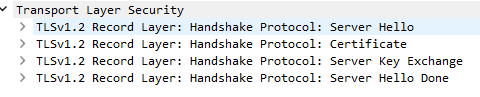
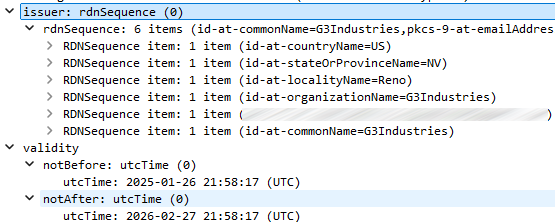
Frames 14-17 are transmitting the data we see reassembled in Frame 18. This is the (RADIUS) Server Hello and contains not only what the server supports or desires but also another critical piece of troubleshooting information (in my opinion); the EAP Certificate. This certificate is presented to the client so it can validate it against a Root CA in its certificate store to verify the RADIUS server.
Another fun fact about this is you can extract a certificate from a capture, download it as a .crt file and open it like any other! However you can still view the information like you would anything else in Wireshark as shown here.
Frames 19 and 20 finish the initial key exchange and make sure the Ciphers on either side are agreed upon.
Finally Frame 21 reports a successful Outer Tunnel creation.
Inner EAP Method
Unfortunately here's where things get obfuscated and we need to rely on the ladder.
The above is the series of exchanges for the inner EAP method. Looking through the frames the only thing to note is under the EAP header you will see whether the frame is a Request or Response. We have 8 frames that match the ladder above so we can assume what they may contain. All the other data is encrypted so nothing to explore there.
4 Way Handshake
At last we’re at the 4 way handshake, 34 frames and 318 milliseconds later. Mind you this was on an unloaded channel and writing this post made me think about a few things:
- How much faster is EAP-TLS
- How slow can things get on a congested network with high speed clients, low speed clients or heavy VoFi traffic
If you need a refresher on the handshake, see my post about this process.
QoS
It is worth mentioning all these frames were sent using QoS level 6 or 7 which is the highest available. This should ensure authentication messages are delivered in a timely manner, but that is not always the case.
Final Thoughts
And there we have it. A rundown of the exchanges needed to connect to a dot1X enabled network using PEAP-MSCHAPv2. Even though I troubleshoot this protocol often, it was still a bit of challenge putting this information into a post that covered the majority of the information without being too lengthy. I hope this helps others when it comes to troubleshooting or those curious about what is going on behind the scenes. With all that said, Ill leave you with a screenshot of the whole process.
















Comments
Post a Comment
Leave a comment...